
Cybersecurity
Stay one step ahead of hackers and protect your company's data and digital assets with our advanced cybersecurity solutions.
Your company safe
against digital threats
Proactive protection, continuous monitoring and a specialized cybersecurity team.
Learn how to protect your companyWhat's at risk isn't just your network, it's your company's reputation.
Reduced teams, a lack of specialists, and tight budgets leave security on the back burner. This exposes your company to potentially costly risks.
Protect your layers
Stay one step ahead of hackers and protect your company's data and digital assets with our advanced cybersecurity solutions.
1. Physical Layer
Most basic layer, involves physical access to devices and infrastructure.
2. Network Layer
It encompasses everything that is exposed via networks — local or internet
3. System Layer
Refers to the operating system and its settings
4. Application Layer
Covers running systems (web apps, internal services, APIs).
5. User Layer
Internal/external users can be attack vectors, especially via social engineering.
6. Cloud Layer
Includes third-party services, SaaS, integrations, and cloud providers.
Partnership with the best companies in the market



Continuous security for your business
Reduce digital risks and keep your operations protected with a comprehensive cybersecurity solution that combines advanced technology and specialized management to ensure peace of mind in any scenario.
24x7 Protection
Continuous monitoring against digital threats.

Immediate Response
Quick action in any incident.
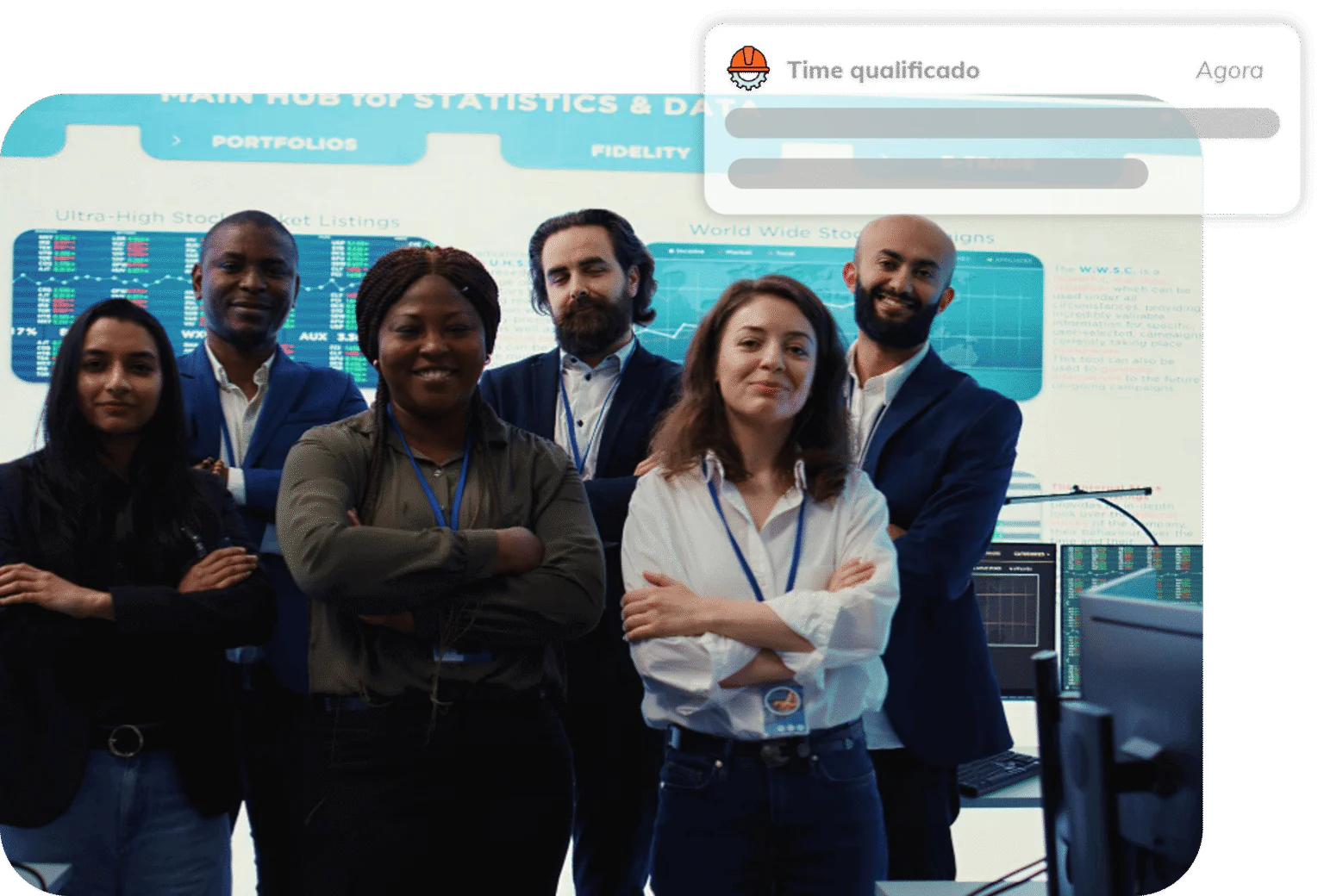
Specialized team
Professionals dedicated to your safety.
A complete cyber protection strategy
Inspired by the NIST model, we structure our operations around pillars that ensure solid and reliable security management. Each step strengthens your company against digital risks and prepares your operations to face future challenges with resilience and efficiency.
1. IDENTIFY
Map your company's critical assets, data, systems, and processes. This is the first step toward understanding risks and knowing where to focus security efforts.
2. PROTECT
Implement access controls, encryption, security policies, training, and other barriers to prevent threats from causing damage.
3. DETECT
Monitor systems in real time, with alerts and analysis tools, to identify suspicious activity as quickly as possible.
4. RESPOND
Have a defined response plan to act quickly in the event of incidents, minimizing impacts and communicating with all involved parties.
5. RECOVER
After an incident, restore services, learn from the incident, and strengthen weaknesses. The goal is to return to operations with resilience.
6. EVOLVE
Continuous improvement and adaptation to new threats.
Over 30 years of experience in information security.
With expertise recognized by major companies in Brazil, we deliver solutions that combine network services, security, and equipment into a single structure.

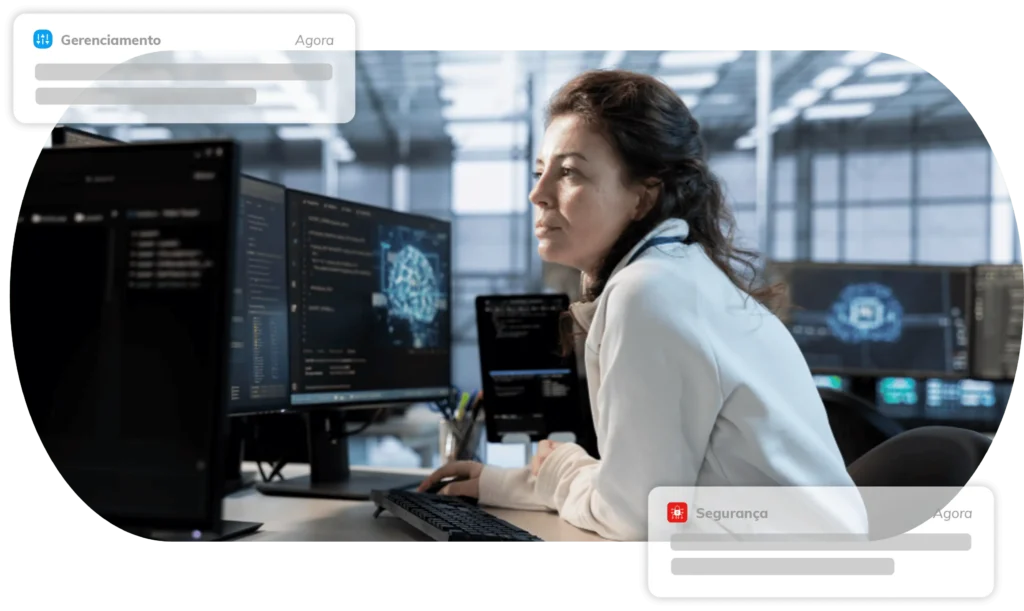
Management
Security

Connect to
future with HIT
Find out how we can transform your business. Talk to one of our experts now!
Get in touch